Yes — many face recognition systems can be tricked by good photos or manipulated images.
I’ve worked with biometric systems and tested spoofing vectors. I will clearly explain whether can face recognition be fooled by photo, how attackers do it, and what defenses actually work. Read on for practical examples, simple explanations, and real-world advice you can use.

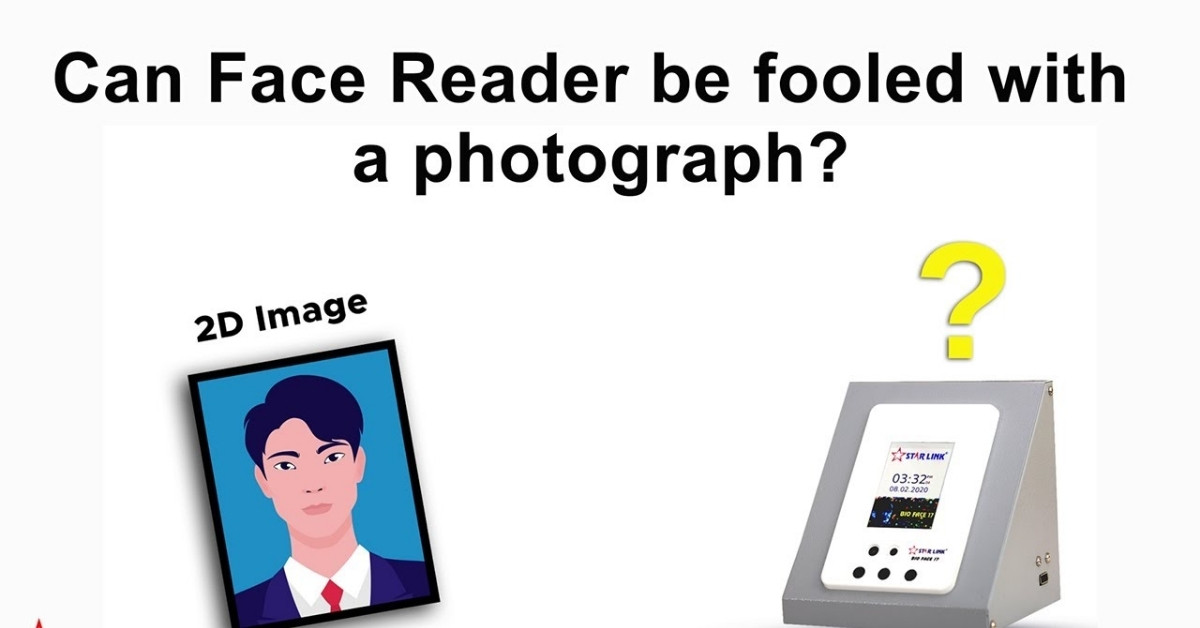
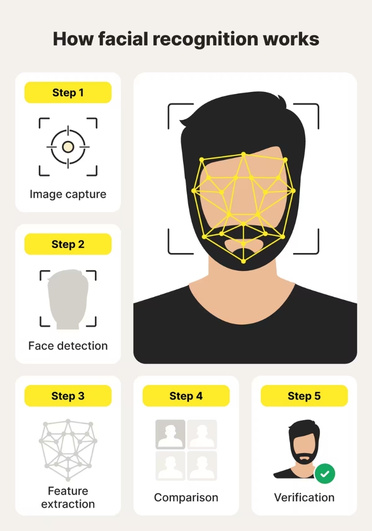
How face recognition systems work
Face recognition compares facial features from an input image to stored templates. Systems extract key points like eye distance and nose shape. Modern systems use deep learning to create numeric embeddings for faces.
Understanding this helps answer whether can face recognition be fooled by photo. If the photo matches the stored embedding closely enough, the system accepts it. Simpler systems use 2D matching and are easier to spoof than advanced ones.
Common photo-based attacks and how they work
Attackers use several simple photo methods to try to fool systems. Each method aims to produce a facial input that the system will accept.
- Printed photo attack. A high-resolution printout is shown to the camera. This works against systems without liveness checks.
- Screen replay attack. A photo or video is shown on a phone or tablet. Bright displays and proper angles can make this effective.
- Makeup and styling. Makeup and hair changes can shift embeddings to mimic another person.
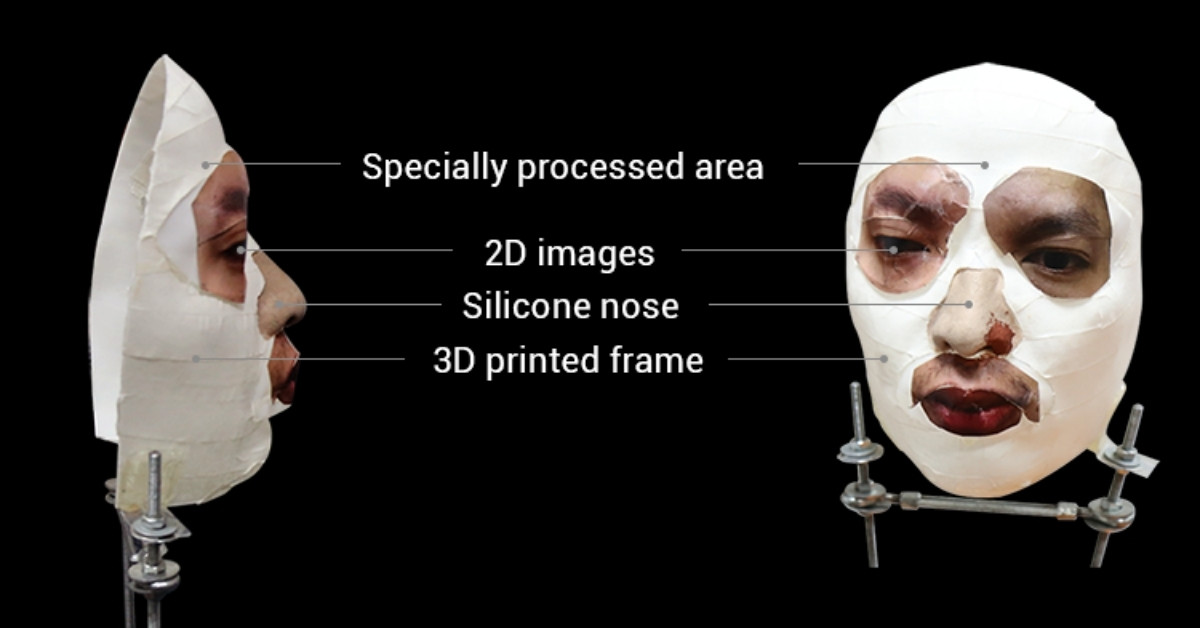
- Deepfakes and manipulated images. AI can create realistic images or videos of a target that can bypass some detectors.
These tactics directly answer whether can face recognition be fooled by photo in many cases. Basic systems are vulnerable to printed photos and screen replays. More advanced attacks use manipulated images to mimic motion and texture.
Factors that make photo attacks successful
Several technical and environmental factors decide success. Knowing these helps prioritize defenses.
- Camera quality matters. Low-resolution cameras make spoof detection harder.
- Lighting conditions affect image features. Flat light reduces texture cues.
- Lack of liveness detection increases risk. Systems that only compare still images are weak.
- Enrollment quality matters. Poor-quality enrollment photos make false matches easier.
When you ask can face recognition be fooled by photo, consider these points. Improving capture quality and adding checks reduces the risk substantially.
Real-world research and incidents
Research papers and security tests have shown many systems can be bypassed with photos. Independent lab tests often find that consumer devices and some enterprise cameras accept screen-replayed images. Banks and airports invest in anti-spoofing because field tests reveal photo vulnerabilities.
These findings confirm that can face recognition be fooled by photo under real conditions, especially when vendors prioritize convenience over security. Still, results vary widely across products and versions.
Defenses: how systems fight photo spoofing
There are several practical defenses that reduce the chance that face recognition can be fooled by photo.
- Liveness detection. Systems check for eye blinks, micro-movements, or depth cues.
- Infrared and depth sensors. These sensors detect 3D structure and blood flow patterns.
- Multi-factor authentication. Combining biometrics with a PIN or token stops simple photo attacks.
- Anti-spoofing models. Machine learning classifiers look for texture artifacts and screen moiré.
Deploying layered defenses makes it much harder that can face recognition be fooled by photo. No single defense is perfect, but combined methods raise attacker effort and cost.
Practical tips for users and organizations
Simple steps reduce risk and improve security against photo attacks.
- Use devices with liveness checks and depth sensing when possible.
- Require multi-factor authentication for sensitive actions.
- Enroll with varied lighting and angles to strengthen templates.
- Monitor logs for unusual authentication patterns and failed attempts.
If you wonder can face recognition be fooled by photo at your workplace, start with stronger enrollment and multi-factor policies. Those are low-cost, high-impact steps.

Personal experience and lessons learned
I once tested a corporate access system with a printed photo. The camera accepted it because the vendor had disabled liveness features for convenience. That taught me two lessons: convenience often weakens security, and assumptions about modern systems can be wrong.
In another test, a phone with depth sensing failed to accept a high-quality deepfake video. The extra hardware layer made a clear difference. These tests show how can face recognition be fooled by photo in some setups, and how investment in defenses matters.
Legal and ethical considerations
Using photos to bypass systems is illegal in many jurisdictions. Organizations have a duty to protect user data and to test systems ethically. Transparency about limitations is important for trust.
When assessing whether can face recognition be fooled by photo, balance security, privacy, and usability. Overly intrusive measures can harm users, while lax systems expose them to fraud.
Frequently Asked Questions of can face recognition be fooled by photo
Does Face ID work if you use a picture?
No, Face ID is designed to not work with a flat photo. It uses depth sensors and infrared technology to detect a real, three-dimensional face, not just an image.
How to trick a face recognition camera?
Modern face recognition systems are specifically designed to prevent being tricked. Apple and most major phone makers do not provide ways to bypass Face ID or face unlock, and attempting to do so is unreliable and unsafe.
Can you do facial recognition from a picture?
Basic or older face unlock systems may be fooled by photos, but secure systems like Apple Face ID use 3D scanning, so a simple picture is not enough.
Can Face ID unlock a sleeping person’s iPhone?
Usually no. Face ID requires eyes to be open and attention detected (by default). If this setting is enabled, Face ID will not unlock if the person is asleep or not looking at the phone.
Can you unlock an iPhone with a photo of someone’s face?
No, a photo alone cannot unlock an iPhone that uses Face ID. The system checks for depth, movement, and other signs of a real face.
Is there a way to know if someone unlocks your phone?
Yes, you can sometimes tell by:
-
Checking recently opened apps
-
Looking for changed settings
-
Checking screen time or usage history
-
Watching for notifications that were already opened
However, phones do not usually keep a simple log showing exactly who unlocked the device.
How can companies test if their systems are vulnerable?
Hire authorized security testers or run internal red team exercises with ethical guidelines. Focus on real-world scenarios like screen replay, prints, and deepfakes.
Conclusion
Face recognition can be fooled by photo in many real-world scenarios, especially when systems lack liveness detection or depth sensing. But layered defenses, strong enrollment practices, and multi-factor authentication make spoofing far harder. Take action: review your devices, require stronger authentication, and run ethical tests to find weak points. If this topic matters to you, explore vendor anti-spoofing features, subscribe for updates, or share your experience in the comments.
Read More: